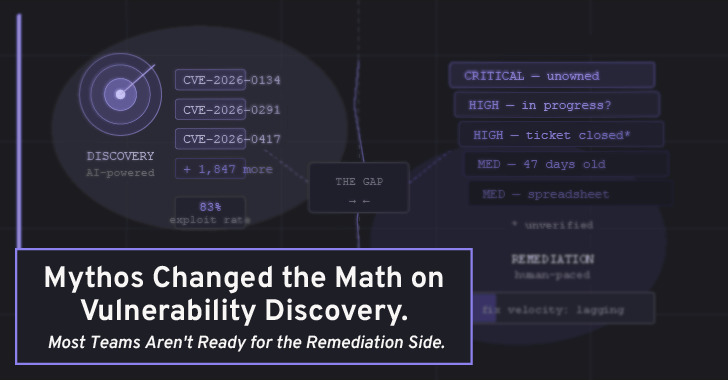
Mythos Changed the Math on Vulnerability Discovery. Most Teams Aren’t Ready for the Remediation Side
Anthropic’s Claude Mythos Preview has dominated security discussions since its April 7 announcement. Early reporting describes a powerful cybersecurity-focused AI system capable of identifying vulnerabilities at scale and raising serious…