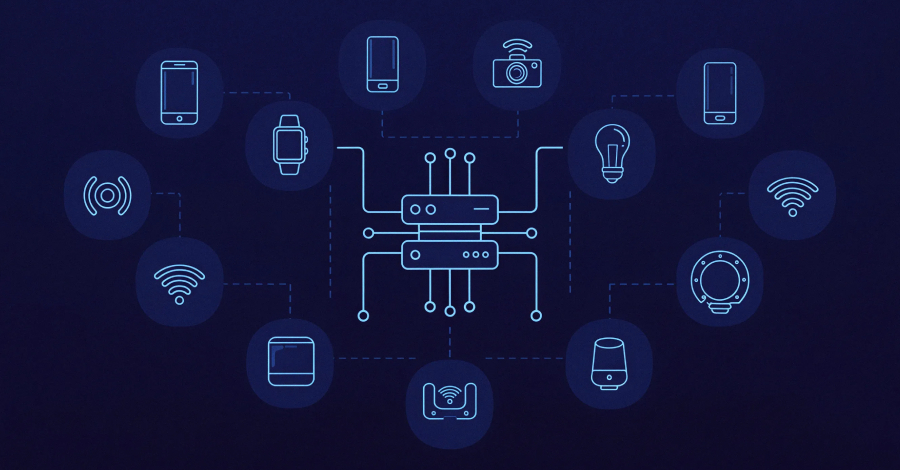
The U.S. Department of Justice (DoJ) on Thursday announced the disruption of command-and-control (C2) infrastructure used by several Internet of Things (IoT) botnets like AISURU, Kimwolf, JackSkid, and Mossad as part of a court-authorized law enforcement operation.
The effort also saw authorities from Canada and Germany targeting the operators behind these botnets, with a number of private sector firms, including Akamai, Amazon Web Services, Cloudflare, DigitalOcean, Google, Lumen, Nokia, Okta, Oracle, PayPal, SpyCloud, Synthient, Team Cymru, Unit 221B, and QiAnXin XLab assisting in the investigation efforts.
«The four botnets launched distributed denial-of-service (DDoS) attacks targeting victims around the world,» the DoJ said. «Some of these attacks measured approximately 30 Terabits per second, which were record-breaking attacks.»
In a report last month, Cloudflare attributed AISURU/Kimwolf to a massive 31.4 Tbps DDoS attack that occurred in November 2025 and lasted only 35 seconds. Towards the end of last year, the botnet is also assessed to have engaged in hyper-volumetric DDoS attacks that had an average size of 3 billion packets per second (Bpps), 4 Tbps, and 54 million requests per second (Mrps).
Independent security journalist Brian Krebs also traced the administrator of Kimwolf to a 23-year-old Jacob Butler (aka Dort) from Ottawa, Canada. Butler told Krebs he has not used the Dort persona since 2021 and claimed someone is impersonating him after compromising his old account.
Butler also said, «he mostly stays home and helps his mom around the house because he struggles with autism and social interaction.» According to Krebs, the other prime suspect is a 15-year-old residing in Germany. No arrests have been announced.
The botnet has conscripted more than 2 million Android devices into its network, most of which are compromised, off-brand Android TVs. In all, the four botnets are estimated to have infected no less than 3 million devices worldwide, such as digital video recorders, web cameras, or Wi-Fi routers, of which hundreds of thousands are located in the U.S.
«The Kimwolf and JackSkid botnets are accused of targeting and infecting devices which are traditionally ‘firewalled’ from the rest of the internet. The infected devices were enslaved by the botnet operators,» the DoJ said. «The operators then used a ‘cybercrime as a service’ model to sell access to the infected devices to other cyber criminals.»
These infected devices were then used to conduct DDoS attacks against targets of interest across the world. Court documents allege that the four Mirai botnet variants have issued hundreds of thousands of DDoS attack commands –
- AISURU – >200,000 DDoS attack commands
- Kimwolf – >25,000 DDoS attack commands
- JackSkid – >90,000 DDoS attack commands
- Mossad – >1,000 DDoS attack commands
«Kimwolf represented a fundamental shift in how botnets operate and scale. Unlike traditional botnets that scan the open internet for vulnerable devices, Kimwolf exploited a novel attack vector: residential proxy networks,» Tom Scholl, VP/Distinguished Engineer at AWS, said in a post shared on LinkedIn.
«By infiltrating home networks through compromised devices—including streaming TV boxes and other IoT devices — the botnet gained access to local networks that are typically protected from external threats by home routers.»
Akamai said the hyper-volumetric botnets generated attacks exceeding 30 Tbps, 14 billion packets per second, and 300 Mrps, adding that cybercriminals leveraged these botnets to launch hundreds of thousands of attacks and demand extortion payments from victims in some cases.
«These attacks can cripple core internet infrastructure, cause significant service degradation for ISPs and their downstream customers, and even overwhelm high-capacity cloud-based mitigation services,» the web infrastructure company said.