China-Linked Red Menshen Uses Stealthy BPFDoor Implants to Spy via Telecom Networks
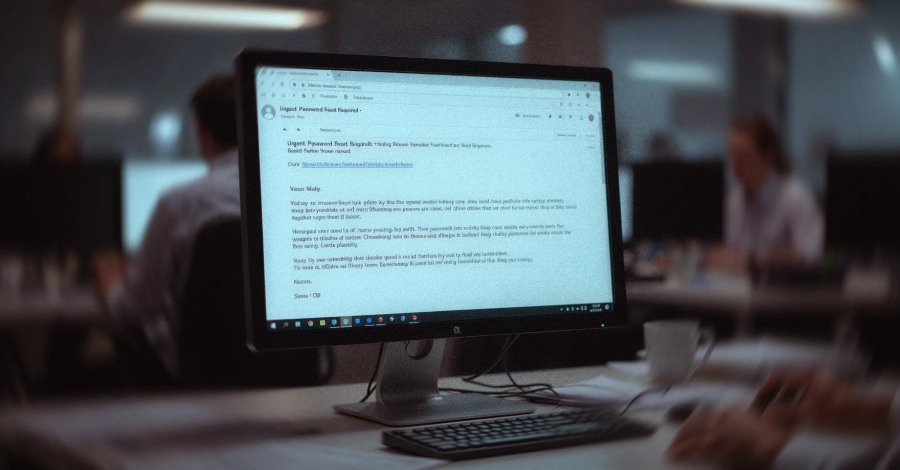
A long-term and ongoing campaign attributed to a China-nexus threat actor has embedded itself in telecom networks to conduct espionage against government networks. The strategic positioning activity, which involves implanting…





![[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks](https://thedigitalfortress.us/wp-content/uploads/2026/03/validate.jpg)