OFAC Sanctions DPRK IT Worker Network Funding WMD Programs Through Fake Remote Jobs
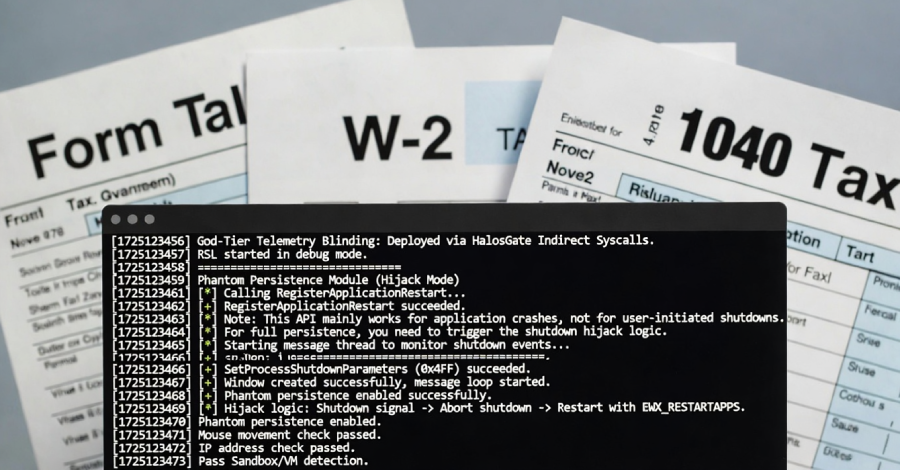
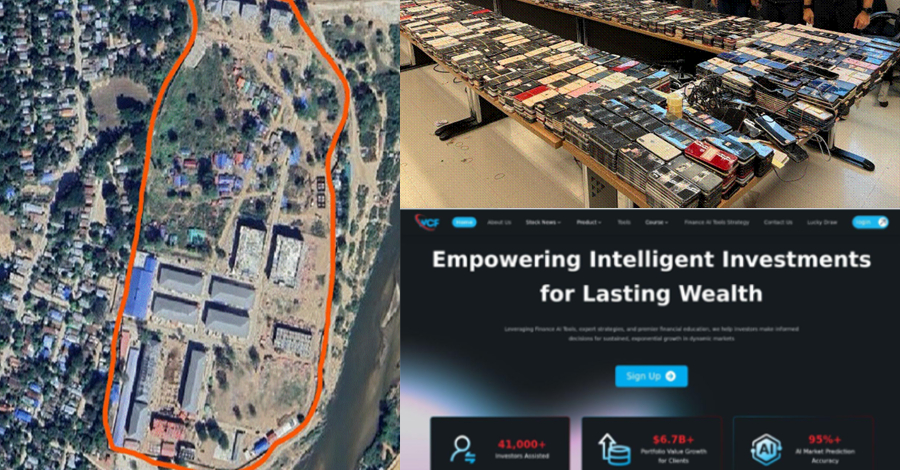
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has sanctioned six individuals and two entities for their involvement in the Democratic People’s Republic of Korea (DPRK)…