New PHP Composer Flaws Enable Arbitrary Command Execution — Patches Released
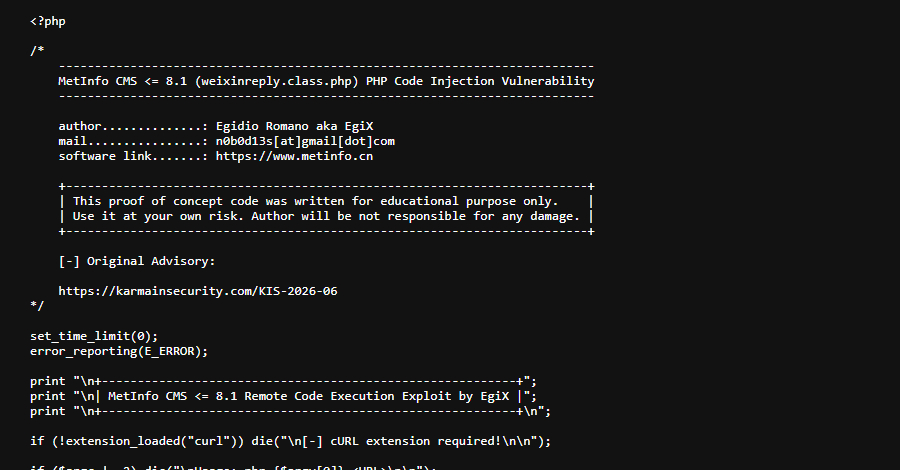
Ravie LakshmananApr 14, 2026Vulnerability / DevSecOps Two high-severity security vulnerabilities have been disclosed in Composer, a package manager for PHP, that, if successfully exploited, could result in arbitrary command execution. The vulnerabilities have been described…